Use Case: microsegmentation
SEGMENT YOUR NETWORK WITHOUT BREAKING APPLICATIONS
Microsegmentation projects stall when traffic visibility is incomplete and policies are based on guesswork. Mugato continuously maps every communication pattern across your infrastructure, so segmentation is grounded in observed behavior, not assumptions.






























How it works
FROM GUESSWORK TO data-driveN rule definition
Five capabilities that turn microsegmentation from a high-risk security project into a data-driven, continuously maintained program.
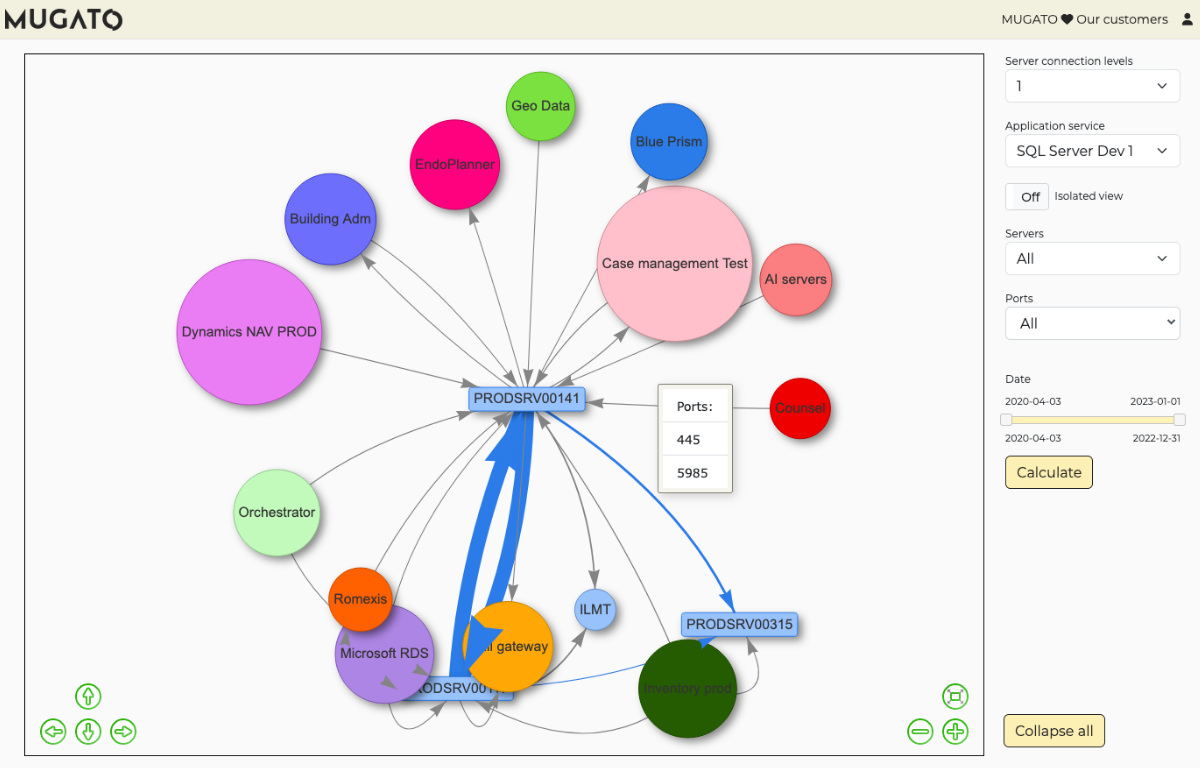
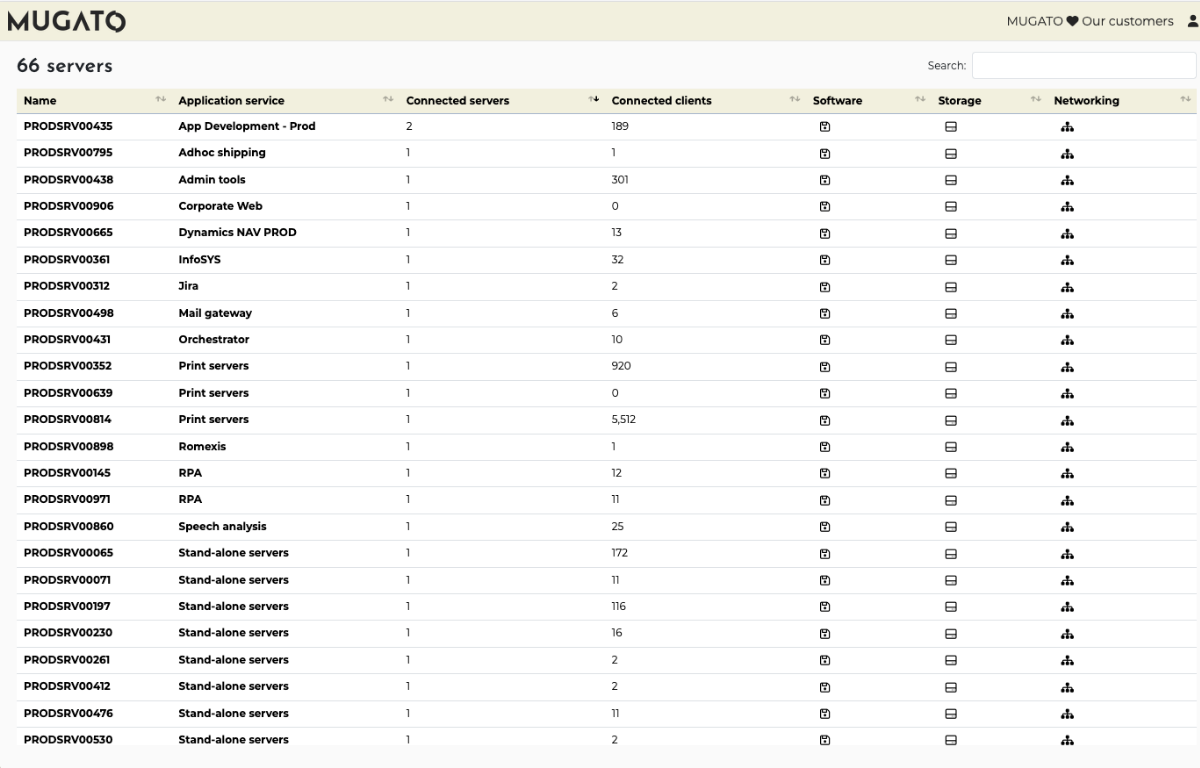
Automated traffic flow discovery
Manual traffic analysis captures only 60–70% of flows. Point-in-time captures miss scheduled processes and periodic activities.
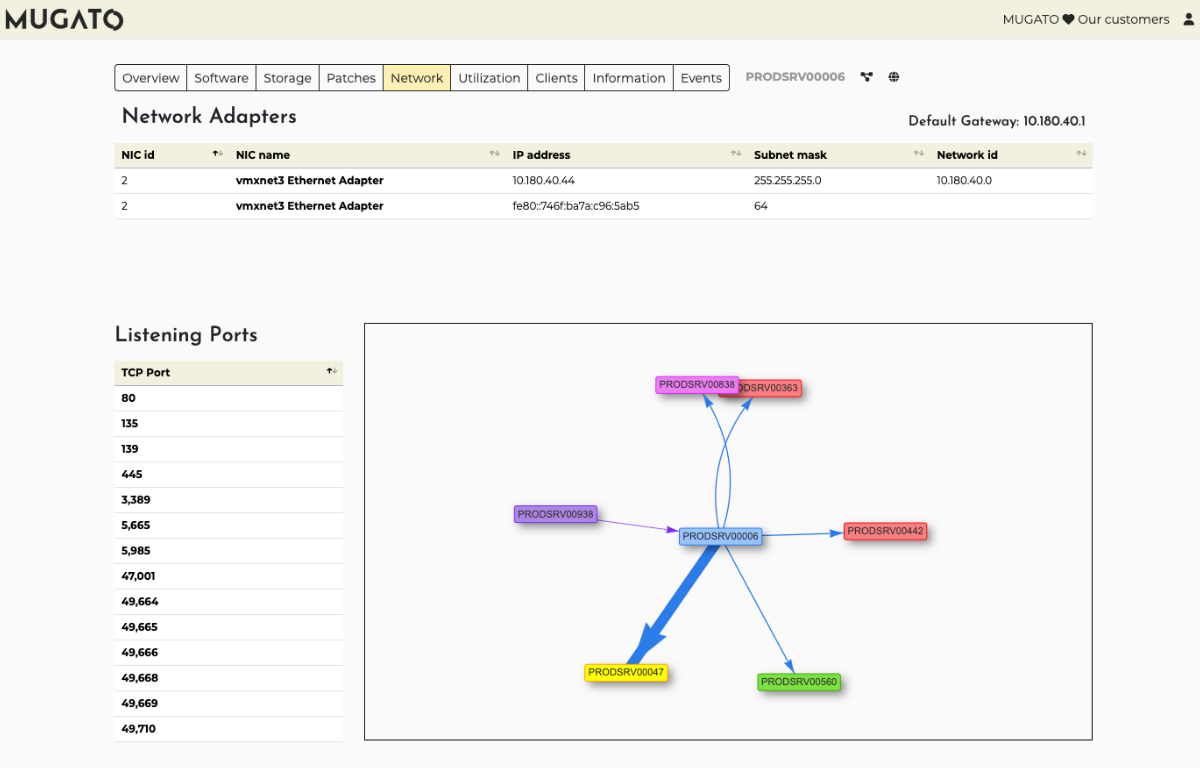
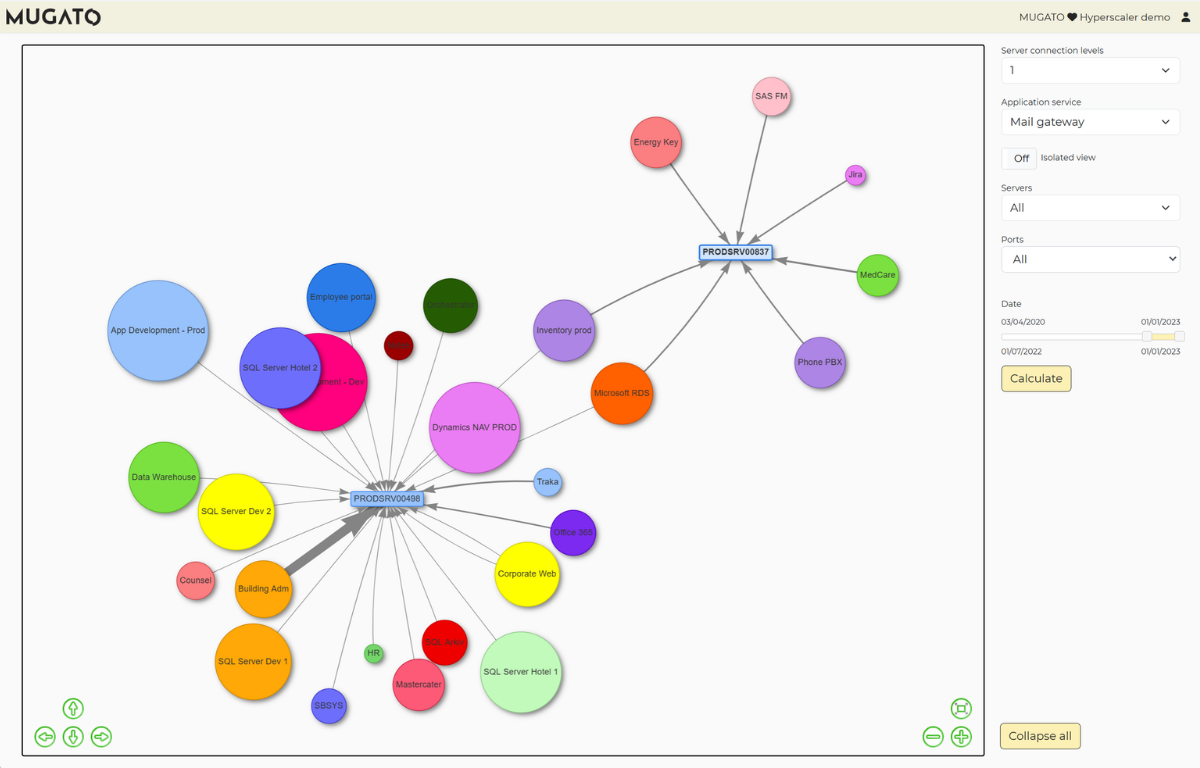
Mugato continuously monitors all network and application communications without agents, capturing actual traffic patterns, protocols, frequency and data volume. You see intermittent processes, scheduled activities and rare but critical communications that point-in-time tools miss. Complete visibility into actual behavior prevents both under-segmentation that leaves security gaps and over-segmentation that blocks legitimate business functions.
Data-driven segmentation rule definition
Rules based on estimates and outdated documentation either break legitimate applications or fail to provide adequate security protection.
Mugato provides dedicated API views and templates that define precise segmentation rules based on observed traffic patterns. The platform tells you exactly what needs to be open, in which direction, between which endpoints, at which port and process level. Output can be formatted according to your segmentation platform, giving you rules grounded in actual behavior, not tribal knowledge.
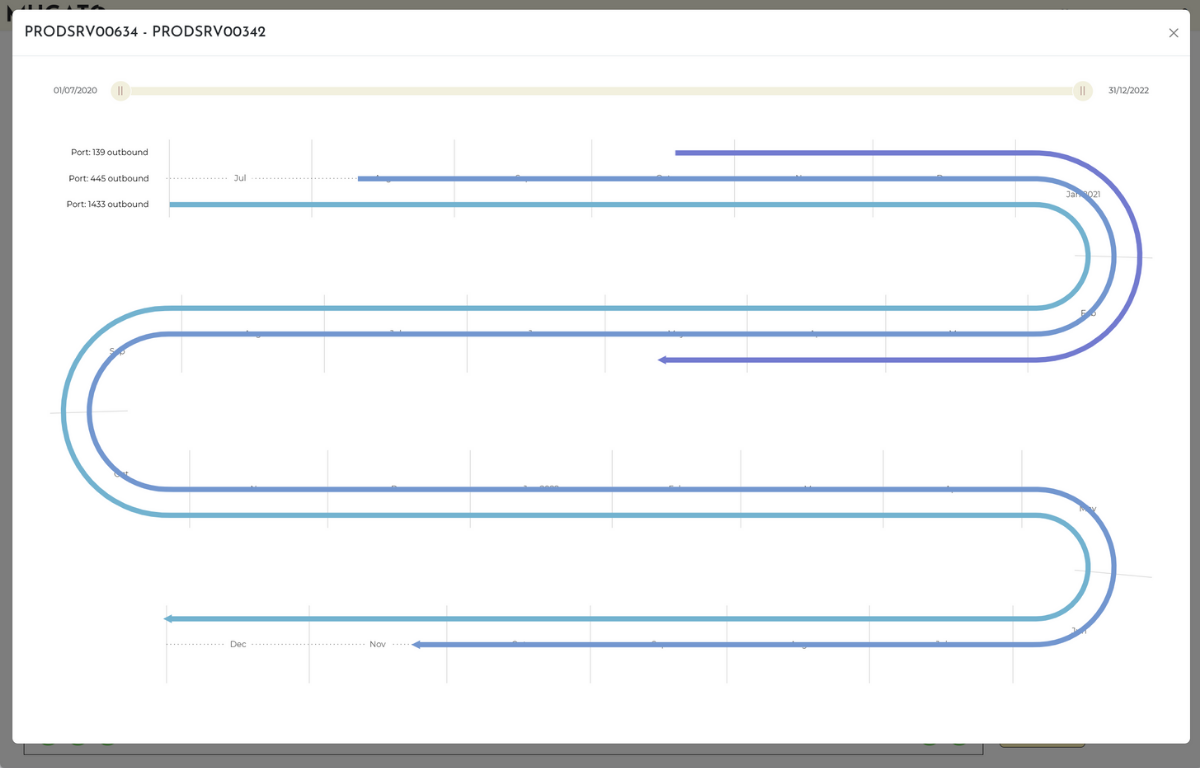
Continuous rule lifecycle management
Static rules become outdated as environments change over months and years, creating security gaps that go undetected.
Mugato’s temporal data shows which connections have stopped, enabling teams to identify and remove stale rules for communications that no longer exist. As new assets deploy and applications evolve, updated traffic data defines the new rules needed. A simple policy of “remove rules for connections not seen in 6–12 months” keeps segmentation from decaying over time.
Optimal segmentation granularity
Teams are stuck between inadequate protection and unmanageable complexity, either too permissive or too restrictive.
Asset-by-asset behavioral analysis determines appropriate segmentation levels based on actual dependencies and business functions. Mugato ensures granular protection where needed while avoiding excessive complexity. Right-sized segmentation achieves security objectives without creating unmanageable policy sprawl or requiring excessive operational overhead to maintain.
Accelerated stakeholder validation
Validating segmentation policies takes months because teams lack concrete data about actual traffic patterns.
Mugato provides application owners with concrete, observed traffic data showing actual communication patterns, frequency and dependencies. Factual evidence replaces manual discovery interviews, shortening validation cycles from months to weeks. Data-driven validation eliminates debate, accelerating deployment timelines while ensuring policies protect without disrupting operations.
Key Outcomes
100%
Continuously capture every network and application communication, including intermittent and scheduled processes that other tools miss.
0
Rules defined from observed behavior ensure legitimate traffic is accounted for before enforcement, eliminating blind segmentation.
75%
Automated traffic discovery and data-driven rule definition compress the discovery and planning phase from months to weeks.
24/7
Rules stay current as your environment evolves, eliminating security gaps from static policies that decay over time.
PAIN POINTS VS. PAINKILLERS
See how Mugato addresses the most common microsegmentation challenges.
What our customers are saying
WHAT OUR CUSTOMERS
ARE SAYING
Ready to get your LIVING it blueprint?
Stay ahead with Mugato: get product updates, event invites, expert insights on IT infrastructure discovery and more. Or let us show you how Mugato can map your entire IT landscape without a single agent.